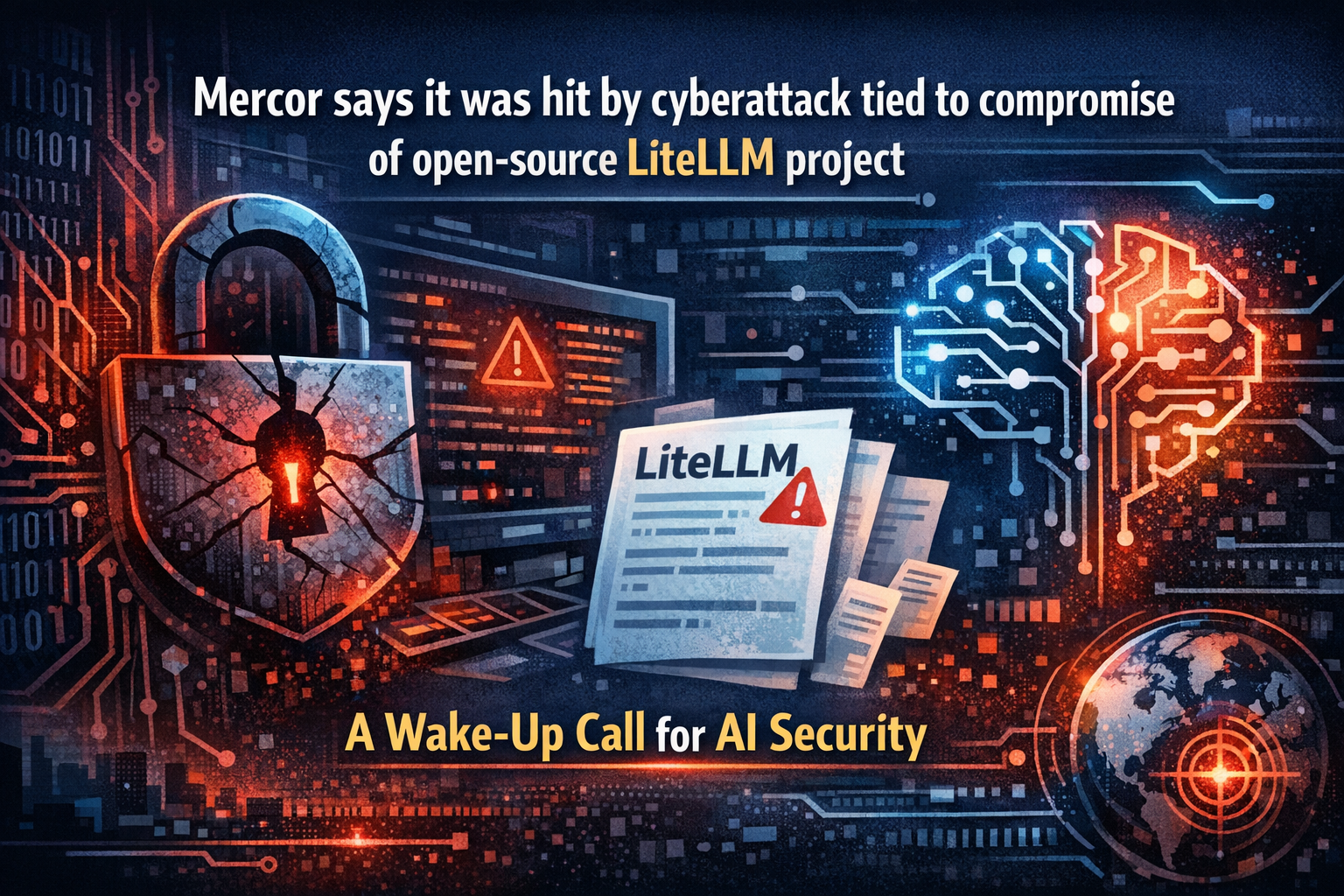
Mercor Hit by Cyberattack Tied to Open-Source LiteLLM Compromise
The digital landscape is constantly evolving, and with the rapid expansion of Artificial Intelligence (AI) technologies, new vulnerabilities are emerging. In a significant development that has sent ripples across the tech community, Mercor, an AI-powered platform for talent acquisition, recently confirmed it was the victim of a cyberattack. Specifically, Mercor says it was hit by cyberattack tied to compromise of open-source LiteLLM project, a revelation that underscores the inherent risks associated with integrating third-party and open-source components into critical systems. This incident highlights a growing concern: the security of the AI supply chain.
This news is more than just a headline; it’s a stark reminder for businesses leveraging AI and developers contributing to the open-source ecosystem. The interconnectedness of modern software development means a weakness in one component can have cascading effects, potentially compromising entire platforms and user data. Understanding the intricacies of this attack, its implications, and preventative measures is paramount for safeguarding future innovations and maintaining digital trust.
Unpacking the Incident: What Happened with Mercor and LiteLLM?
According to Mercor’s official statements, the breach originated from a compromise within the open-source LiteLLM project. LiteLLM is a popular, lightweight Python package designed to simplify calls to various large language models (LLMs) like OpenAI, Azure, Cohere, and others. Its appeal lies in its ease of use, cost tracking, and unified API, making it a go-to choice for developers building AI-powered applications.
The precise nature of the compromise within LiteLLM is still being investigated, but such incidents often involve malicious code injection into the project’s repository, a compromised maintainer account, or a sophisticated social engineering attack. Once compromised, users integrating the affected version of LiteLLM into their applications unknowingly incorporate the malicious payload. This allows attackers to potentially exfiltrate data, gain unauthorized access, or disrupt services within the systems that depend on the compromised library.
For Mercor, the impact meant a breach that they are actively working to contain and remediate. This incident serves as a critical example of how even widely trusted open-source tools, when compromised, can become conduits for sophisticated cyberattacks. The reliance on such projects is immense in the fast-paced AI development world, making the integrity of these components absolutely crucial.
The Anatomy of Open-Source Supply Chain Attacks in AI
The concept of a software supply chain attack is not new. From the SolarWinds incident to the Log4j vulnerability, we’ve seen how a single weak link in the software delivery process can be exploited to gain access to countless downstream users. However, the rise of AI introduces new layers of complexity and risk.
- Deep Interdependencies: AI applications often rely on a deep stack of libraries, frameworks, and models, many of which are open-source. Tracing every dependency, especially transitive ones, is a monumental task.
- Novel Attack Vectors: Beyond traditional code vulnerabilities, AI systems can be targeted through model poisoning, data manipulation, or adversarial attacks against the models themselves.
- Rapid Development Cycles: The fast pace of AI innovation often prioritizes speed over stringent security checks, leading to shortcuts and potential oversights.
- Trust in Communities: While open-source fosters collaboration and transparency, it also relies heavily on the good faith and security practices of maintainers and contributors worldwide. A single malicious actor can undermine this trust.
The fact that Mercor says it was hit by cyberattack tied to compromise of open-source LiteLLM project highlights that even popular and well-regarded tools are not immune. Developers integrate LiteLLM for its utility, assuming its robust community and open nature equate to inherent security. This incident challenges that assumption and forces a re-evaluation of how we assess risk in our AI technology stacks.
Mitigating Risks: Fortifying Your AI and Open-Source Supply Chain
Preventing future incidents like the one experienced by Mercor requires a multi-faceted approach, combining proactive security measures with robust incident response capabilities. Here are practical steps businesses and developers can take:
1. Comprehensive Dependency Auditing and Management
- Software Bill of Materials (SBOMs): Generate and maintain SBOMs for all your applications. This provides a clear inventory of all components, including open-source libraries like LiteLLM, and their versions.
- Vulnerability Scanning: Regularly scan your dependencies for known vulnerabilities using tools like Snyk, Dependabot, or OWASP Dependency-Check. Integrate these scans into your CI/CD pipeline.
- Supply Chain Security Platforms: Consider specialized platforms that monitor the integrity of your open-source supply chain, looking for suspicious changes in repositories or packages.
2. Implement Strict Security Best Practices
- Least Privilege: Ensure that your applications and the users running them only have the minimum necessary permissions.
- Network Segmentation: Isolate critical AI infrastructure and sensitive data from less secure components or public networks.
- Secure Coding Standards: Adhere to secure coding guidelines and conduct regular code reviews to catch potential vulnerabilities before deployment.
- Authentication and Authorization: Implement strong authentication mechanisms and granular access controls for all AI services and underlying infrastructure.
3. Vigilance and Proactive Monitoring
- Threat Intelligence: Stay informed about the latest cyber threats, especially those targeting AI technologies and popular open-source projects. Reputable sources like BleepingComputer provide invaluable insights.
- Runtime Monitoring: Implement solutions that monitor the behavior of your AI applications in production, looking for anomalous activities that might indicate a compromise.
- Regular Updates and Patching: Keep all software, including operating systems, frameworks, and libraries, up-to-date with the latest security patches.
4. Internal Link: Enhance Your Cybersecurity Posture
For more detailed strategies on protecting your digital assets, explore our comprehensive guide on cybersecurity best practices. Understanding the foundation of security is key to building resilient AI systems. The incident where Mercor says it was hit by cyberattack tied to compromise of open-source LiteLLM project underscores this need for foundational strength.
Lessons from Mercor: A Call for Collective Responsibility
The incident involving Mercor and LiteLLM is a stark reminder that cybersecurity is a shared responsibility. The open-source community, individual developers, and large enterprises all have a role to play in fortifying the digital ecosystem. For developers contributing to open-source projects, stringent security hygiene, multi-factor authentication for repository access, and diligent code reviews are paramount. For companies consuming these projects, a robust vendor risk management program that extends to open-source dependencies is crucial.
Moreover, fostering a culture of security within organizations, where every team member understands their role in preventing and responding to cyber threats, is more important than ever. Regular training, simulations, and clear incident response plans can significantly reduce the impact of a breach. As the world continues its rapid adoption of AI, the attack on Mercor serves as a pivotal case study, urging us all to prioritize security from the ground up.
Another Internal Link: Future of AI Security
To delve deeper into the evolving landscape of AI and its security challenges, visit our article on the future of AI security. Understanding these trends is essential for preparing for what lies ahead, especially given that Mercor says it was hit by cyberattack tied to compromise of open-source LiteLLM project.
The Road Ahead: Building Resilient AI Ecosystems
The cyberattack on Mercor, stemming from a compromise in the LiteLLM project, underscores a critical truth: no software is entirely invulnerable. However, by adopting proactive security measures, fostering a culture of vigilance, and embracing collaborative security practices, we can significantly reduce the attack surface and enhance our resilience against sophisticated threats. This means investing in tools, training, and processes that scrutinize every layer of our AI applications, from the foundational open-source libraries to the deployed models.
Moving forward, the AI industry must learn from incidents like this. It’s not enough to simply leverage powerful open-source tools; we must also contribute to their security and develop robust strategies for managing their inherent risks. This collective effort will ensure that the incredible potential of AI can be realized without compromising the security and trust of users and businesses alike. The incident where Mercor says it was hit by cyberattack tied to compromise of open-source LiteLLM project should be a catalyst for stronger, more secure AI development practices globally. For further insights on defending against supply chain attacks, you can refer to expert analysis from sources like Dark Reading’s supply chain security section.
The journey to secure AI is continuous, but with every incident, we gain valuable insights that drive us towards more robust and reliable systems. Let this serve as a powerful reminder that security is not an afterthought, but an integral part of innovation.
#Cybersecurity
#AISecurity
#OpenSourceSecurity
#SupplyChainAttack
#Mercor
#LiteLLM
#DataBreach
#TechSecurity
#DigitalTrust